The new-age Manhattan Project: How do we protect today’s secrets from tomorrow’s quantum computers?
Will Hurd believes the next global arms race is already underway.
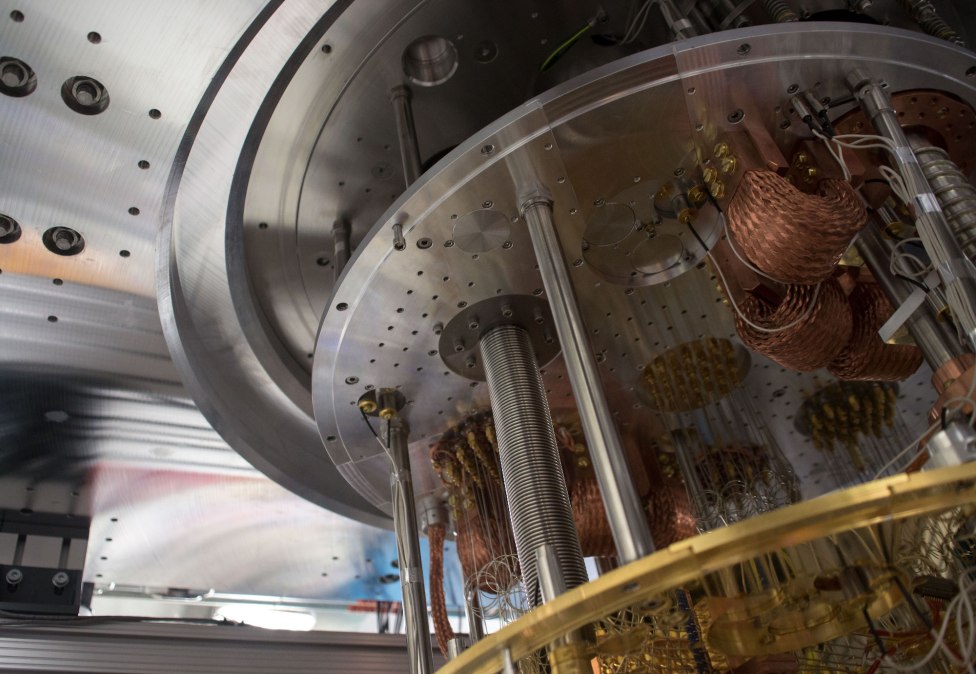
This time around, the hardware is a bit more esoteric. The U.S., its allies and its foes are investing billions to develop a technology that could define the age: quantum computing.
The Texas Republican congressman compares the peril posed by the development of this futuristic technology with the anxieties of the atomic age. As quantum computing moves from theory to practice, he told FedScoop, it’s time for the U.S. to start taking it seriously.
“I talk about the threat of quantum more than I talk about the opportunities,” Hurd said. “One, it’s to make sure that people understand the importance of this. It’s sometimes hard to understand or recognize the need for significant financial investment in something when the payoff is several years away.”
There are two reasons why it’s difficult the communicate the urgency surrounding quantum computing, he said: explaining what it is and predicting when it’s coming. And while predictions for mainstream arrival range between 10 and 30 years, the consensus is that when usable quantum computers do arrive, the encryption methods utilized today to protect our most guarded secrets will be obsolete.
And for that reason, public and private stakeholders are not only focusing on the benefits of the impending quantum age, but also on defending against its darker side.
“My feeling is that now’s the time, while we still have some lead time before the technology is really here, where we need to start preparing the rules of the road, especially standards and practices, particularly for quantum cryptography,” said Arthur Herman, a senior fellow at the Hudson Institute.
How quantum encryption works
Modern computer encryption operates by scrambling information with complex algorithms. If you have the cryptographic key — basically, the password — undoing the math is easy. If you don’t have the key, it’s still theoretically possible, although prohibitively time-consuming, to crack the encryption with brute-force computing.
A big leap in computing power, however, could potentially render that kind of encryption useless.
That’s why quantum computers are drawing so much attention. Because their processors work with quantum bits, or qubits, that exist as both a one and a zero at the same time, they potentially possess significantly more computing power. They could attack modern cryptographic methods at a speed impossible with current machines.
“It would break them fast enough that we’d have to scrap those ones and use different cryptosystems that hopefully aren’t vulnerable to quantum computers,” said Dustin Moody, a mathematician in the National Institute of Standards and Technology’s Cryptographic Technology Group.
To ensure that networks will be protected in the future, NIST has reached out to private stakeholders to help develop new cryptographic standards that are resistant to quantum computers’ problem-solving power. In the short term, what’s at stake is the ability for billions of existing computers to continue to encrypt information securely, including those across critical infrastructure systems.
In November, NIST accepted 69 publicly submitted algorithms for its Post-Quantum Cryptography competition, which the agency will evaluate to incorporate into future standards.
“We hope to work with the larger crypto community around the world so we can get as many people working on this as possible,” Moody said, adding that the algorithms are available for public analysis as well.
NIST projects it will analyze the submitted algorithms over the next three to five years before issuing draft standards two years later. While there is still time to develop these defenses, technology companies are edging closer to the point where quantum computers have the power to solve problems classical computers can’t — a threshold referred to as quantum supremacy.
Whatever the case, post-quantum cryptography is hardly an exact science at this point, and the algorithms that will be utilized are based on the current research done in a field that is constantly advancing.
“What we rely on is that certain algorithms have been discovered, so we know certain things that [a quantum computer] can do,” Moody said. “There’s really no guarantee that a quantum computer can’t break these problems necessarily. It’s just that nobody has been able to find a way to do it so far, which might not sound great, but that’s kind of actually what we rely on today. It’s really the same paradigm, it’s just that we are putting quantum computers into the mix as well.”
NIST’s plan to produce standards within the next seven years might not be aggressive enough, said Scott Totzke, CEO of ISARA Corp., a Canadian quantum security company.
“I think that’s a bit of a risky timeline,” he said. “If you look at where a lot of the research in the industry starts to coalesce right now, we can make a case for the quantum computer that is a cryptographic threat could be here as early as 2026.
“If you say five years before we have standardized crypto, that takes us to 2023. If you think about this as an [original equipment manufacturer] who’s got to look at those standards, make changes to the product portfolio and get those to market, well that’s going to take another two years,” Totzke added. “And when you start talking about large, complex infrastructure like say the Department of Defense public key infrastructure that manages identity for 3.5 million civilian contractors and enlisted personnel, that doesn’t change in a year.”
The new Manhattan Project
Part of the urgency surrounding quantum computing comes from the heavy investment the U.S. and competing powers have so far put into developing the technology.
In September, the Chinese said they were building a $10 billion quantum applications research facility as a sign of the importance of developing a strategic edge in the field. Russia has also been testing various applications, including the first quantum-secured blockchain capable of resisting a brute force attack from a quantum computer.
One way Herman said that the U.S. could speed the development of quantum technology is by negotiating information-sharing agreements between the federal government, the private sector and allies, like Canada, Australia and New Zealand, on quantum research, developing a new-age Manhattan Project similar to the World War II initiative that built the atomic bomb.
“I think that this is a push that’s going to have to come in two directions: one from Congress and one from the executive branch, particularly from the White House,” he said. “Big technological pushes like that require stewardship from the top.”
Hurd, a former CIA officer and chairman of the House Oversight Subcommittee on Information Technology, said he would support intelligence sharing between allies on quantum technology. It’s important to bring attention to the issue, he said, as well as leverage the power of federal research bodies like the National Science Foundation.
“This is something that is important and with such a big challenge, we are going to have to leverage the resources of all of our friends and do this thing together,” Hurd said.
While awareness about quantum computing is growing, Totzke said it’s understandable that the technology is not an immediate focus for Congress and the White House. It should become part of the strategic planning of the nation’s critical infrastructure, he said.
“You know that there are a hundred other things that are going on, probably a thousand, that a CISO or a CIO needs to be considering,” he said. “But the other element of it is, because we have to go through such a long migration from where we are today, to in essence updating every piece of technology so that it’s quantum-safe or ensuring that a future infrastructure will allow for quantum-safe and classical cryptographic algorithms to be used concurrently, that is not a trivial project.”




