Ex-HHS CIO says agency was hit with over 8 billion scanning efforts during March 2020 DDOS-style attack
The Department of Health and Human Services was hit with more than eight billion scanning attempts over 18 hours in a distributed denial-of-service-style attack in 2020, according to the agency’s former chief information officer.
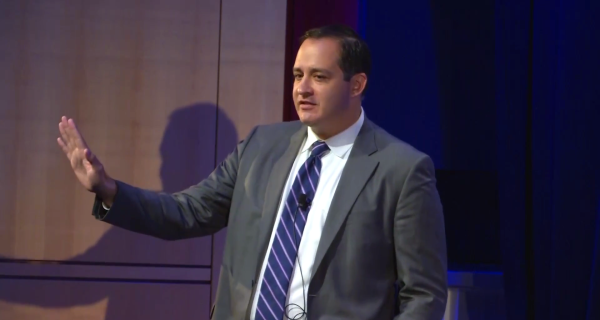
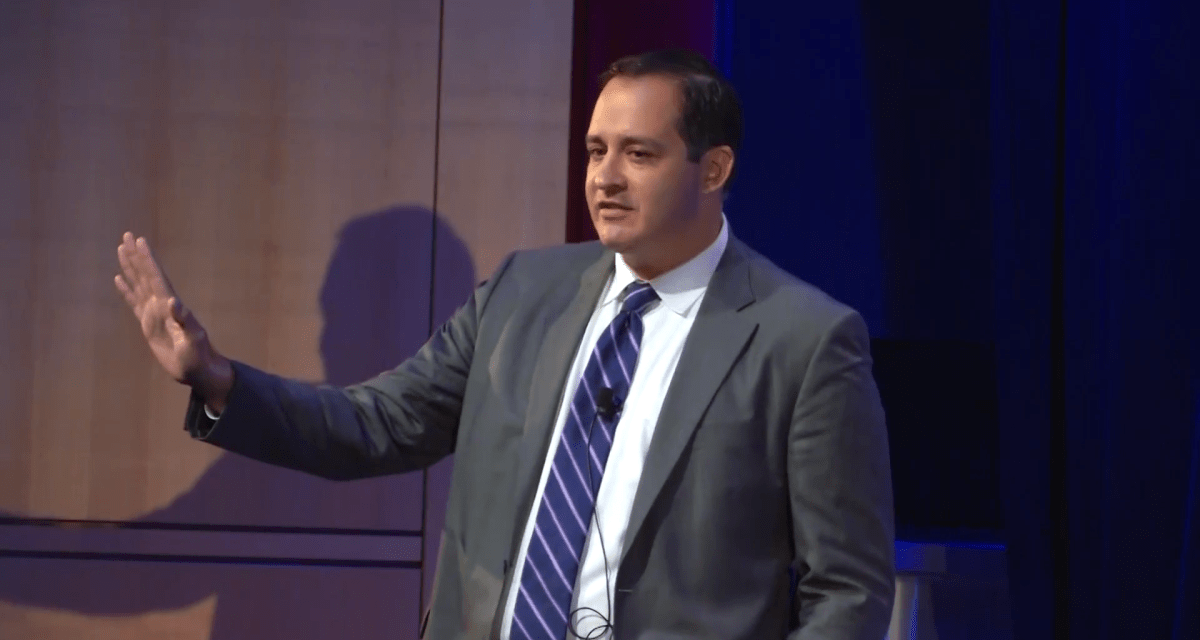
In an interview with FedScoop, José Arrieta said that attackers were waiting for the agency to lower its perimeter firewall and clear its cache — because the network was backloaded with about 50 million packets slowing it down — to access the department’s network.
HHS was hit with a serious DDOS-style attack on March 15, 2020, as malicious actors sought to take advantage of the agency’s pandemic move to full telework to infiltrate its network.
“And when we did [lower the firewall] they were trying to embed themselves in the HHS network so that, when we went on full-on telework, they could exfiltrate data,” Arrieta told FedScoop. “And we would have no visibility or understanding if it was normal telework or whether it was an enemy combatant that was actually trying to steal data.”
According to Arrietta, HHS’ network remained functional because the agency had already upgraded its firewalls, Trusted Internet Connections capacity at multiple locations, server capacity and Virtual Private Network capability for telework.
Scanning attacks are used to gather network information ahead of sophisticated cyberattacks. Commonly used scanning techniques to gather computer network information include IP address scanning, port scanning and version scanning.
Additional details about the cyber threat faced by HHS at the height of the coronavirus pandemic come after multiple former senior officials challenged key findings of a quashed watchdog report into the cybersecurity of COVID-19 data analysis systems launched at that time.
Officials speaking to this publication said that the report, which was rescinded last month by the HHS inspector general, failed to take into account the speed at which agency leaders were having to respond to the situation, the lack of available high-quality data, and the cybersecurity measures the CIO’s office implemented in light of the March 15 attack.
Two officials briefed on the investigation refuted its findings, saying the functions provided by the technology to senior medical decision makers in a short time period outweighed any potential cyber risks.
HHS did not respond to a request for comment.